Secure.
Simplify.
Scale.
At Serapic, we empower businesses to control access, prevent unauthorized use, and enhance security through our Identity & Access Management (IAM) platform, built to scale for businesses of all sizes




Make the right first impression, collect all the info as a user signs up for the first time.
Coding is not required to make an app. You can create fully customized apps that can be downloaded onto any smartphone, tablet, or computer using Jotform's free no-code app builder.

Make the right first impression, collect all the info as a user signs up for the first time.
Coding is not required to make an app. You can create fully customized apps that can be downloaded onto any smartphone, tablet, or computer using Jotform's free no-code app builder.

Our Mission & Vision
At Seraphic, we believe that in today's digital landscape, security and simplicity should go hand in hand.Seraphic is on a mission to revolutionize how businesses manage and secure their digital identities and resources. Our Identity & Access Management (IAM) platform is at the core of our vision, providing businesses with the tools to protect their sensitive data, simplify user management, and ensure compliance with ever-evolving regulations.
What’s Next for Seraphic
Expansion Areas
Frequently Asked Questions
FAQs address key aspects of Seraphic Minds
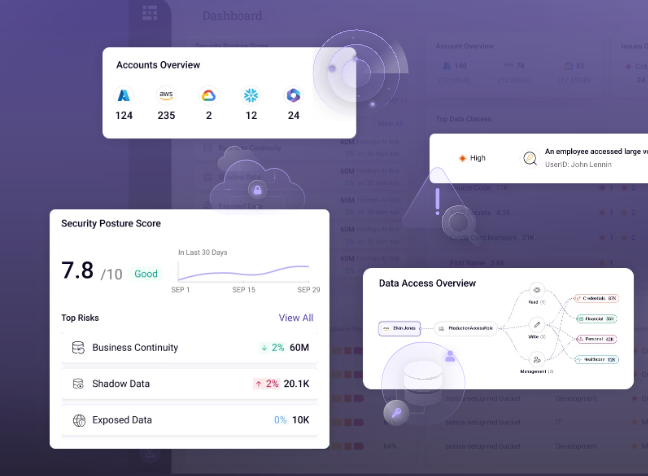
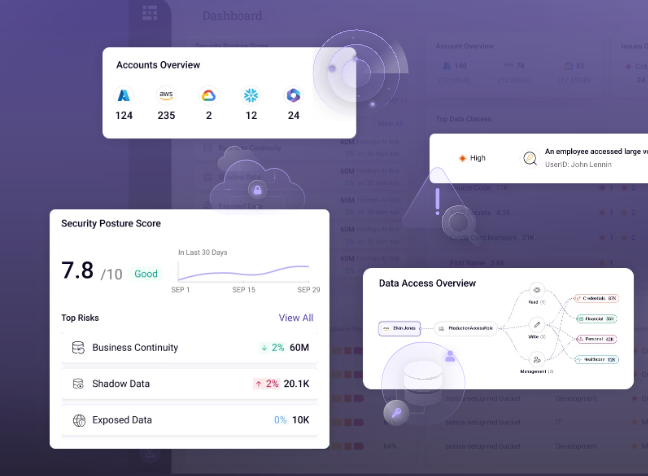
Serapic’s DSPM platform provides automated data discovery, real-time risk assessment, and continuous monitoring of your data security posture. With AI-driven insights, we help companies pinpoint vulnerabilities, secure data access, and prevent misconfigurations before they lead to breaches.Key Tools:Automated Risk Identification: Real-time assessment of misconfigurations, over-privileged users, and insecure data access.AI-Powered Remediation: AI-backed automation to take immediate corrective actions, like revoking risky permissions or encrypting sensitive data.
Serapic implements a zero trust architecture that requires continuous authentication for every access request to data, eliminating the risk of insider threats and unauthorized access.Key Tools:Behavioral Analytics: Detect anomalies in user behavior to prevent unauthorized data access.Granular Access Control: Strict enforcement of least-privilege principles and continuous verification.Serapic implements a zero trust architecture that requires continuous authentication for every access request to data, eliminating the risk of insider threats and unauthorized access.Key Tools:Behavioral Analytics: Detect anomalies in user behavior to prevent unauthorized data access.Granular Access Control: Strict enforcement of least-privilege principles and continuous verification.Serapic implements a zero trust architecture that requires continuous authentication for every access request to data, eliminating the risk of insider threats and unauthorized access.Key Tools:Behavioral Analytics: Detect anomalies in user behavior to prevent unauthorized data access.Granular Access Control: Strict enforcement of least-privilege principles and continuous verification.
Serapic offers advanced insider risk management through behavioral analytics and AI-driven detection of abnormal activities within your data environment.Key Tools:Real-Time Monitoring: Continuous tracking of user activity to detect unusual or risky behavior.Automated Alerts: AI-driven alerts when potential insider threats are detected, allowing for quick response.
Serapic offers automated data classification, where AI is used to automatically label sensitive data and enforce security policies based on its classification.Key Tools:AI-Powered Classification: Automatically classify sensitive data (PII, financial data, etc.) to apply the correct security policies.Policy Automation: Ensure that classified data follows compliance standards (GDPR, HIPAA, CCPA).
Still have a question?
Connect with Us

